Environment Red Hat Enterprise Linux (RHEL) 4 5 6 7 Issue How to monitor the permission change and ownership change of a particular directory or file? How to configure auditd to find how a file was modified in Red Hat Enterprise Linux? What tool can audit files at a directory level? How do I monitor files or […]
Category: Linux
VI Editor cheat sheet
vi mode commands Command Action k Move one line upwards l Move one character to the right h Move one character to the left w Move one word to the right W Move one word to the right past punctuation b Move one word to the left B Move one word to the left past […]
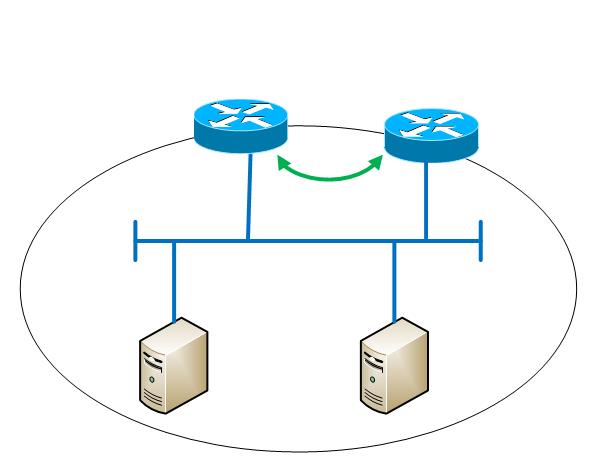
Centos 7/RHEL 7 LVS HAPROXY KEEPALIVED
Credit: CertDepot: Presentation For this tutorial, you need 2 virtual/physical servers for the load-balancers and 2 virtual/physical servers to load-balance. In addition to the 4 IP addresses needed by the servers themselves, a fifth virtual IP address (VIP) is necessary. The two load-balancers and the VIP need to be in the same network segment. Piranha […]
Linux Multiple Gateways
example use: one gateway to send outgoing traffic. Other traffic use the other gateway. Two Gateways below for example: gw1 : 172.26.2.100 gw2 : 172.26.3.100 Create a virtual interface which will be used by processes that need to send traffic to gateway gw2: $ ifconfig eth0:1 172.26.3.209 Create a definition and give a name to […]
Digital Black Hole /dev/null
anything sent to /dev/null will be eaten like a digital black hole ONLY try this on test VM if you want to destroy ! do not cut and paste on live or production systems – use at your own risk. For testing purposes only – DESTRUCTIVE COMMAND! mv / /dev/null
NMAP – scan for unused or down IP’s
nmap -v sn -n 192.168.3.0/23 -oG – | awk ‘/Status: Down/{print $2}’ -sn (No port scan) . This option tells Nmap not to do a port scan after host discovery, and only print out the available hosts that responded to the scan. This is often known as a “ping scan”, but you can also request […]